Managed Security Solutions
You’re in good company.






“This was the best installation we’ve ever had.”
We’re proud to say that a client shared this with us recently. So many things need to happen for a successful install, with literally hundreds of moving parts to pay attention to and control. We strategize, we plan, and we prepare… And then the install is where the rubber meets the road. And so when it all goes smoothly, and a client tells us it’s the best they’ve ever experienced, we smile a little bit and then keep working hard.
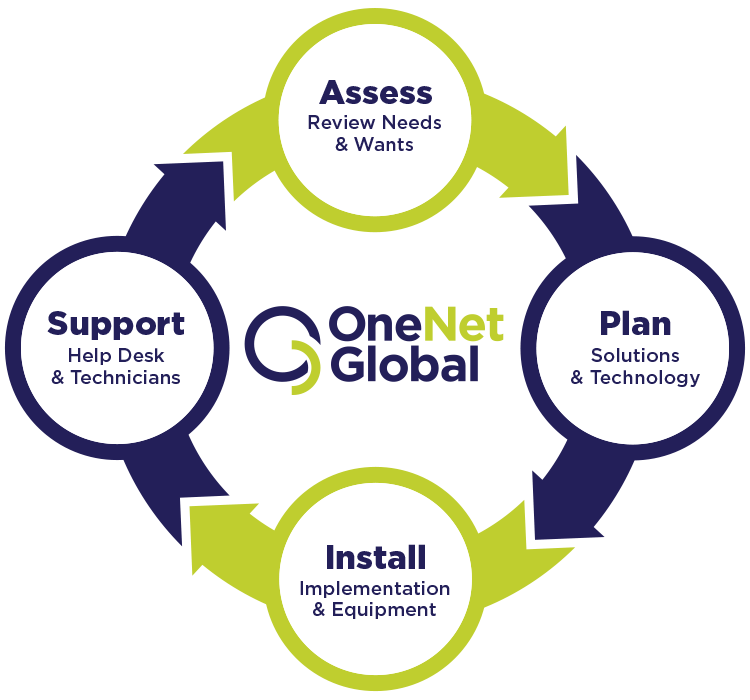
MANAGED TELECOM SOLUTIONS
MULTI.
Multi-carrier. Multi-service. Multi-location. Multi-state. Multi-country. If communicating effectively between multiple locations is critical to your business, then we’re the perfect “multi” partner for you.
ONE.
One help desk. One phone number. One bill. One Managed Telecom partner. One team you can count on. OneNet Global.
MANAGED IT SOLUTIONS
CUSTOM CRAFTED
That’s not something you typically hear from a technology company. When it comes to Managed IT, custom crafted solutions are hard to come by. They take more time to develop, and they take a lot more work to create. But ask yourself this: Are your needs the same as everyone else’s? Will a cookie cutter approach work for you? Probably not. Whether we fully manage your network, or go with a co managed solution, we will fully work with you so that your needs are met.
We understand that no two customers are alike, and our custom crafted approach to Managed IT reflects that. We work hard to understand your needs today and plan for tomorrow, to develop a strategy that addresses your present and your future. Each solution is different based on your individual needs, and from install to support, we’re by your side.